As promised in the last post, I am back with the solutions to the problem we left. There are couple of solutions when collection of sets is given explicitly. If for example, sets S1 to Sn are given with the constraint that all and only members together from any set should be able to unlock the secret. Given n such sets, there are two solution which are similar in some sense.
First solution, can make the unlocking as hard as possible. That is, there is a brute force way to unlock, even if you are not authorized. In this, we share a secret as n tuple, each co-ordinate in the tuple is of length 1024 ( making it possibilities ). That is for each set, you have 1024 bit. Choose a secret S and make n copies of it. Now, for each element of the tuple ( that is for each set Si) you can use the XOR method that we mentioned in the first post of the series.
Second solution, again uses tuples, but instead of using the XOR one can use the polynomials. Choose, different polynomial for each co-ordinate of the tuple such that the polynomial constant is secret S. This is again described in the first post.
However, when sets are not given explicitly, the size of the tuple becomes very large if one goes on to enumerate all possible sets which can unlock. The solution which ramprasad had in mind is using circuit with threshold gates. is a k-threshold gate which becomes one when k or more of the inputs are set to one.
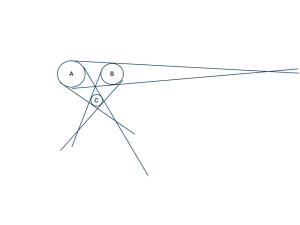
Now, let us see how the circuit for the counter example mentioned in the last post would look like.
The example was as follows. group of 8 persons. 5 or more should be able to unlock the secret. If there are 4, then they would be able to unlock only if there are even of them from the first half ( in turn, there are even of them from each half 🙂 ).
The circuit would look like this
where LTh and RTh denotes threshold gates for the left and the right half. Note that if we want to enumerate the sets there are
sets. In comparision, having such a circuit is a very efficient solution 🙂